Web Applications Authentication Brute Force | Practical Demo [Screenshots] | Brute Force Website Login | How To
This post is meant to elucidate web application brute forcing by providing a practical demo.
Read up on Authentication Brute Force here.
OWASP testing guide is your friend in Web Application Hacking.
How To Brute Force Website Login | Web Application Hacking Example | Authentication Brute Force
We have a ‘Test’ website running on 172.19.17.120. I have created a Test account on it with username ‘pranshu’ and password ‘p’. (As we are playing the part of a penetration tester, during the test we will assume we do not know the password)
It has a login form requiring a ‘username’ and ‘password’. HTTP POST Request Parameters are used.
Set up Burpsuite Proxy to intercept traffic between your browser and the server page you will be trying to brute force [Read up on Burpsuite]
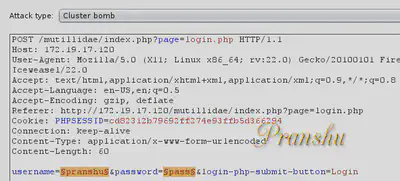
Then send these to Burpsuite ‘Intruder’ to be attacked
The attack we will use is ‘Cluster Bomb’
The highlighted parameters in the image above are the ones which will be bruteforced.
In case you already know ‘username’, “un-highlight” it, meaning Brute Force Password only. Since I already know the username is ‘pranshu’, I will try to brute force the password and set username as ‘pranshu’
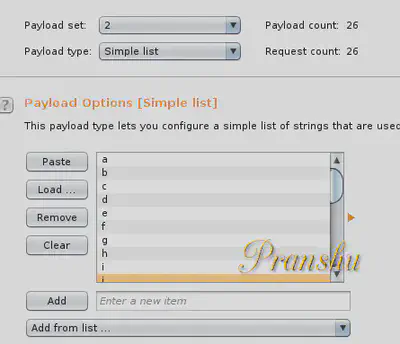
Payload type is a ‘simple list’ of characters ‘a,b,c,d….z’ [which we will use as possible passwords]
Execute the attack. It will set the username to ‘pranshu’ and go through the ‘simple list’, trying every possible alphabet as password. All will recieve HTTP code 200 (OK)
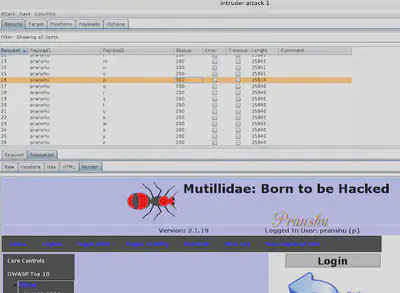
Except one where the payload was set to ‘p’. It received HTTP code 302 (Redirect)
If you know HTTP codes you know that 302 (Redirect) means that the webpage is trying to send us to another page. As a penetration tester, I would guess that the re-direction is occurring because of successful login (redirect to ‘Home’ page or something)
To verfiy this, I ‘render’ the ‘response’ in Burp suite and sure enough I see I am logged in as user ‘pranshu’.
In this case, I have used BurpSuite but you can use ‘Brutus’ or ‘Hydra’ for such online brute force password cracking.