KringleCon | Badge Manipulation Question 6 | CTF Challenge Solution
Question 6: Badge Manipulation
The objective for this challenge is simple – we need to bypass the authentication mechanism. The way the authentication works is the machine “Scanomatic” scan a QR code on an employee badge and grants access depending if the QR code matches a proper record in the back-end database. So we immediately think of the possibility of an SQL injection attack here since the back-end database is involved. There are two ways of entering the QR code into the system: 1) scan it using the integrated webcam or 2) upload a QR code image. 2) is a much safer option since I am uncomfortable with the idea of enabling webcam access for a CTF website. Also, I have a webcam protector physically blocking my webcam and I have no intention of taking it down for this challenge.
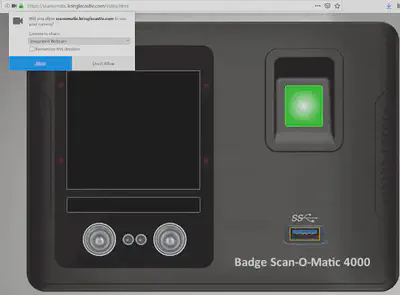
So we need a way to inject SQL queries into the database. But first we need to have the SQL queries in the form of a QR code. This online QR code generator is pretty helpful. It accepts text input and converts it into QR code and provides the relevant image. We can then upload this image to the web interface.
So let us begin as we begin all SQL injection attacks. Test it with a single quote ’ injected into the database and see if we can generate an error message. Sure enough, we see an error message that tells us all that we need to know.

It shows us a long error message which clearly identifies that the database type is MariaDB and that the SQL query is:
select first\_name,last\_name,enabled from employees where authorized = 1 and uid='{}' "limit 1".format({uid})
Now that is all that we needed to inject some valid SQL in there that can bypass authentication. So what do we need to bypass authentication? Basically, the account should be authorized and enabled.
To make the query valid we can use the # to comment out the rest of the query after our point of injection. Our point of injection is the field ‘uid’. So we can the end uid field with single quote ’ followed by a #. So we try the following injection:
' #
That gives us a ’no authorized user account found’ error message.

Alright, so we need to provide it an always True condition to nullify the where authorized = 1 part of the query. So let’s try the following injection:
' or 1=1 #
The 1=1 part in our injection is the always true and nullifies the authorization = 1 part. When we try this injection, we are presented with a new error message: ‘authorized user account has been disabled’.

We need one final bypass for the ’enabled’ part of the SQL query. So we need to formulate our injection such that both authorization and enabled are bypassed. Let’s try the following:
' or enabled = 1 #
This ensures that it shows us a record of the first employee where the account is currently enabled. Finally, we are able to bypass authentication and are greeted with an ‘access granted’ message that reveals the control number that we need to solve this challenge. Note that after this injection, our SQL query would basically take this form:
select first\_name,last\_name,enabled from employees where authorized = 1 and uid='' or enabled = 1 #
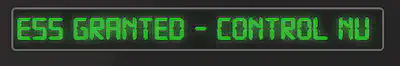
! Answer: 19880715