Hacking Neighbours Wifi Password
Wireless Network Penetration Testing - Step by Step How To
Table of Contents
Disclaimer: For educational purposes only: This is meant merely to exhibit the dangers of using poor wireless security. Please note that prior to beginning the test you should seek explicit consent from the owner if the access point does not belong to you.
Background
While conducting authorized wireless testing, I noticed 4 wireless access points belonging to the target network. 3 of these were using WPA/WPA2 and I was in no mood for a dictionary attack on WPA handshake. It takes a long time and success isn’t guaranteed. I found one access point using WEP security which is great since WEP is an outdated protocol with poor security.
Attacking WEP
I tested penetrating this WEP access point using the same Aircrack-ng Suite of tools as I have mentioned in my previous post.
- Discovered the WEP AP having SSID ‘dlink’ (notice the weak signal power from neighbor’s house to mine)
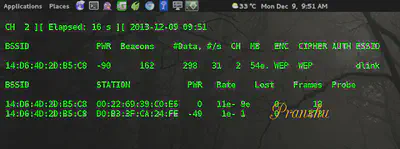
- Collected the required number of data packets from the WEP network. Meanwhile, I used
aireplay-ng --arpreplayto increase the data rate since I am not a patient soul.
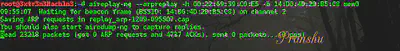
- Saved the data packets in a file called
neighbor-01.capand cracked the password usingAircrack-ng’s dictionary attack module.
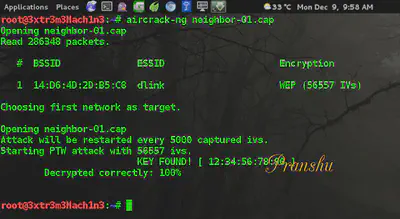
The key for the neighbor’s wifi turned out to be: 1234567890 – easy to guess; just what I expected from someone using WEP security in 2014.
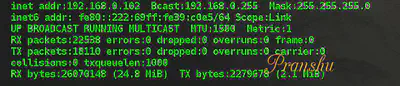
- I connected to the wifi using the decrypted key, it allocated an IP to me using DHCP:
192.168.0.102.
Note: If you want a better step by step on how to hack a WiFi, check out my previous post here.
-
I was connected to the Internet!
-
Since I was part of the target network now, curiosity got the better of me and I decided to scan the network and see who else is connected. I found 2 devices on the network:
- my personal machine
- the Dlink router itself (
192.168.0.1)
None of the neighbor’s own devices were connected to the network at the time.
Accessing router admin panel
nmap told me that the dlink router had an open port 80, which reminded me to check out the control panel of this dlink device.
- So I fired up my browser and went to
192.168.0.1:80which opened the login panel for dlink access point control panel.
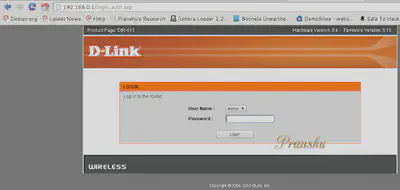
-
Quick Google search revealed that defaults for login on dlink devices are: username:
adminand password:blank. -
Tried logging in with defaults and got access to the control panel.
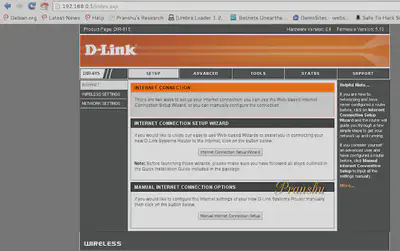
Again, bad security practice: leaving defaults unchanged!
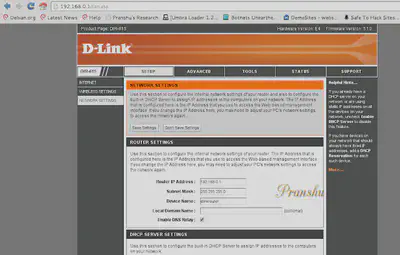
Upgrading router firmware
- Due to weak signals from the access point, I decided to upgrade their firmware and see if it made a difference.
The Current firmware of the neighbor’s wifi was 5.10. I checked for latest Firmware available. It was 5.13.
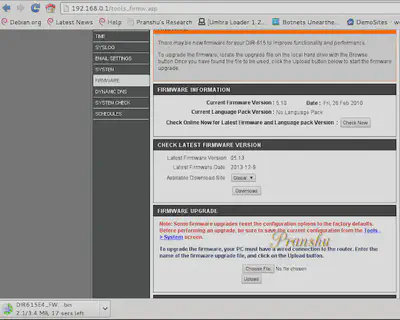
I downloaded the upgrade on my machine (DIR********.bin)
-
I made a backup of the configuration of the access point before upgrading. I saved backup
config.bin'to my laptop from the neighbor’s wifi. -
I went ahead and upgraded the firmware. I uploaded the
DIR****.binfrom my laptop to the access point and it went for a reboot.
I lost access to the WiFi after the upgrade.
I figured the new upgraded firmware changed the password for the WiFi now and I couldn’t connect to it anymore. Moreover, since I lost access to the Internet now along with the WiFi, I couldn’t Google the default password for the upgraded firmware anymore (didn’t have an alternative route to the Internet at the time).
And I couldn’t crack it either because this time no one–not even the neighbor himself–would be able to authenticate to the WiFi with the new unknown password after the firmware upgrade and hence no data packets would be generated and I will have nothing to crack.
-
I fired up ‘Airodump-ng’ again and noticed that the firmware upgrade simply changed the access point security to “open”, ie, no password is required to connect to it.
-
I connected to the “Open” wifi and restored the Configuration settings using the
config.binbackup I made earlier.
Conclusion
I manually selected WPA2 security and provided the same password as used earlier by my neighbor (1234567890). Later that evening, I provided my neightbor a small wireless assessment report, making the recommendation to upgrade WiFi security to WPA2 and choosing a strong password.
Finally, please note that I had explicit consent from the owner before commencing this test. If you do not have such permission, please try it on your own access point.